With the rise of IoT devices and cloud-based solutions, secure remote access has become a critical aspect of modern infrastructure management. RemoteIoT Web SSH provides a web-based interface that allows users to establish secure shell (SSH) connections without the need for complex configurations or additional software installations. This tutorial will cover the essential steps to get started with RemoteIoT Web SSH, including setting up your account, configuring devices, and exploring advanced features that can streamline your workflow.
Throughout this comprehensive guide, we will explore various aspects of the remoteiot web ssh tutorial, providing detailed instructions and expert tips to help you maximize your remote management capabilities. From basic setup procedures to advanced security configurations, this article aims to equip you with the knowledge and skills necessary to efficiently manage your devices from anywhere in the world.
Table of Contents
- What is RemoteIoT Web SSH and How Does It Work?
- How to Set Up RemoteIoT Web SSH: Step-by-Step Guide
- Why Choose RemoteIoT Web SSH Over Traditional Methods?
- Advanced Features and Configurations
- Is RemoteIoT Web SSH Secure Enough for Sensitive Data?
- How to Troubleshoot Common Issues in RemoteIoT Web SSH
- RemoteIoT Web SSH Tutorial: Best Practices for Optimal Performance
- Frequently Asked Questions About RemoteIoT Web SSH
What is RemoteIoT Web SSH and How Does It Work?
RemoteIoT Web SSH is a cutting-edge solution designed to provide secure remote access to devices through a web-based interface. Unlike traditional SSH methods that require dedicated client software and complex configurations, RemoteIoT Web SSH simplifies the process by offering a user-friendly platform accessible from any modern web browser. This innovative approach to remote device management has revolutionized how businesses and individuals interact with their IoT infrastructure.
Read also:What Does Ig Mean In Chat Understanding Its Meaning And Usage
The core functionality of RemoteIoT Web SSH revolves around establishing encrypted connections between your local machine and remote devices. When you initiate a session through the web interface, the system creates a secure tunnel that protects your data transmission from potential threats. This process involves several key components:
- Authentication mechanisms to verify user identity
- Encryption protocols to secure data transmission
- Session management tools for efficient connection handling
- Access control features to define user permissions
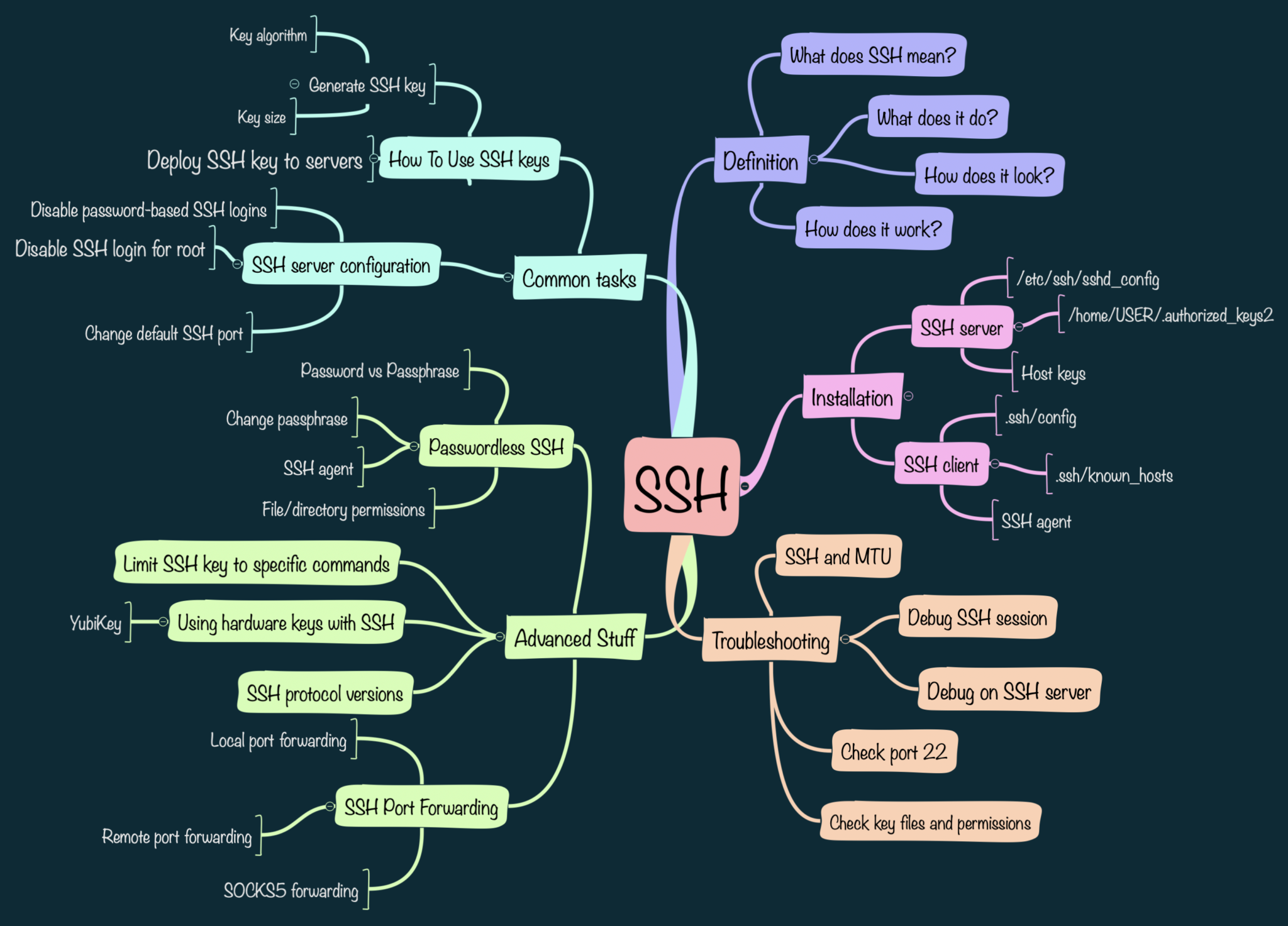
Key Components of RemoteIoT Web SSH Architecture
Understanding the underlying architecture of RemoteIoT Web SSH can help users appreciate its robust security features. The system comprises multiple layers of protection and functionality:
- Web interface layer for user interaction
- Authentication server for identity verification
- Encryption module for secure communication
- Device management dashboard for centralized control
How Data Flows Through the System
When you access a device through RemoteIoT Web SSH, your commands travel through a sophisticated pipeline of security measures. First, your browser establishes a connection with the RemoteIoT servers using HTTPS protocol. The system then authenticates your credentials through multi-factor authentication before creating an encrypted tunnel to the target device. This seamless process ensures that your commands reach their destination securely while maintaining optimal performance.
How to Set Up RemoteIoT Web SSH: Step-by-Step Guide
Getting started with RemoteIoT Web SSH requires careful preparation and systematic execution. This section will guide you through the complete setup process, ensuring you establish a secure and functional remote access environment. The procedure involves several crucial steps, each contributing to the overall security and efficiency of your remote management system.
Initial Account Configuration
Begin by creating your RemoteIoT account through their official website. During registration, you'll need to provide essential information and set up your initial security parameters. Pay special attention to the following:
- Choose a strong, unique password
- Enable two-factor authentication (2FA)
- Configure your preferred notification methods
- Set up your organization's access policies
Device Preparation and Integration
Before connecting your devices to RemoteIoT Web SSH, ensure they meet the necessary requirements:
Read also:Is Mark Levin Sick Exploring The Truth Behind The Rumors
- Verify that devices support SSH protocol
- Update firmware to the latest version
- Configure local firewall settings to allow SSH traffic
- Generate and register SSH keys through the RemoteIoT interface
Establishing Secure Connections
With your account and devices prepared, you can now establish your first remote connection:
- Log in to your RemoteIoT Web SSH dashboard
- Select the target device from your registered list
- Initiate the connection through the web interface
- Verify the security certificate before proceeding
Remember to test your connection thoroughly and document any issues you encounter during the initial setup. This information can prove invaluable for troubleshooting and optimizing your remote management experience.
Why Choose RemoteIoT Web SSH Over Traditional Methods?
When evaluating remote access solutions, RemoteIoT Web SSH stands out for several compelling reasons. Unlike conventional SSH methods that require dedicated client software and complex network configurations, RemoteIoT offers a streamlined, web-based approach that significantly reduces setup time and technical overhead. This modern solution addresses many of the challenges associated with traditional remote access methods while introducing innovative features that enhance both security and usability.
Advantages of Web-Based SSH Access
The web-based nature of RemoteIoT Web SSH provides numerous benefits that traditional methods struggle to match:
- Cross-platform compatibility: Access your devices from any modern web browser without installing additional software
- Centralized management: Control multiple devices through a single, unified interface
- Automatic updates: Benefit from continuous security improvements without manual intervention
- Enhanced security: Leverage enterprise-grade encryption and authentication protocols
Cost-Effectiveness and Scalability
Traditional SSH methods often require significant investment in infrastructure and maintenance. RemoteIoT Web SSH, on the other hand, offers a more economical solution that scales effortlessly with your growing needs. The pay-as-you-go pricing model eliminates upfront costs while providing flexibility to adjust resources based on actual usage patterns. Additionally, the cloud-based architecture ensures that you can expand your remote management capabilities without worrying about hardware limitations or complex network configurations.
Advanced Features and Configurations
While RemoteIoT Web SSH excels in basic remote access functionality, its true potential lies in its advanced features and configuration options. These sophisticated capabilities allow power users to optimize their remote management experience while maintaining robust security measures. From automated workflows to custom scripting, the platform offers numerous tools to enhance productivity and streamline complex tasks.
Automation and Scripting Capabilities
One of the most powerful aspects of RemoteIoT Web SSH is its support for automation and custom scripting:
- Scheduled tasks: Automate routine maintenance and monitoring tasks
- Custom scripts: Execute complex workflows through predefined scripts
- Event triggers: Set up automated responses to specific system events
- API integration: Connect with third-party services for enhanced functionality
Advanced Security Configurations
For organizations with stringent security requirements, RemoteIoT Web SSH offers several advanced configuration options:
- Implement role-based access control (RBAC) for granular permission management
- Configure custom encryption protocols for enhanced security
- Set up detailed audit logging for comprehensive activity tracking
- Establish geofencing rules to restrict access based on location
Is RemoteIoT Web SSH Secure Enough for Sensitive Data?
Security remains a paramount concern when dealing with remote access solutions, particularly when handling sensitive information. RemoteIoT Web SSH addresses these concerns through a multi-layered security approach that combines industry-standard protocols with innovative protective measures. This comprehensive security framework ensures that your data remains protected throughout the entire remote access process.
Core Security Features
The platform incorporates several fundamental security mechanisms:
- End-to-end encryption using AES-256 and TLS 1.3 protocols
- Multi-factor authentication with support for hardware tokens
- IP whitelisting and blacklisting capabilities
- Real-time threat detection and automated response systems
Compliance and Certifications
RemoteIoT Web SSH maintains compliance with major industry standards, including:
- GDPR for data protection and privacy
- ISO 27001 for information security management
- HIPAA for healthcare data security
- PCI DSS for payment card industry compliance
These certifications, combined with regular security audits and penetration testing, ensure that RemoteIoT Web SSH meets the highest security standards for handling sensitive information.
How to Troubleshoot Common Issues in RemoteIoT Web SSH
Even with the most robust systems, occasional issues may arise when using RemoteIoT Web SSH. Understanding how to effectively troubleshoot these problems can significantly reduce downtime and maintain optimal performance. This section provides a comprehensive guide to identifying and resolving common challenges that users may encounter during their remote management operations.
Connection Problems and Solutions
When facing connection issues, follow these systematic troubleshooting steps:
- Verify internet connectivity on both local and remote devices
- Check firewall settings and ensure necessary ports are open
- Validate SSH service status on the target device
- Review authentication credentials and permissions
Performance Optimization Techniques
To enhance your RemoteIoT Web SSH experience, consider these optimization strategies:
- Enable connection caching for frequently accessed devices
- Adjust session timeout settings to match usage patterns
- Utilize local terminal emulation for faster command execution
- Implement bandwidth throttling for large data transfers
RemoteIoT Web SSH Tutorial: Best Practices for Optimal Performance
Maximizing the effectiveness of RemoteIoT Web SSH requires adherence to established best practices that ensure both security and efficiency. These guidelines, developed through extensive experience with remote management solutions, can significantly enhance your overall experience while maintaining robust protection for your devices and data.
Security Best Practices
Implement these security measures to fortify your remote access environment:
- Regularly rotate SSH keys and passwords
- Enable and configure detailed logging
- Implement least privilege access principles
- Conduct periodic security audits and vulnerability assessments
Operational Efficiency Tips
Streamline your remote management operations with these practical suggestions: