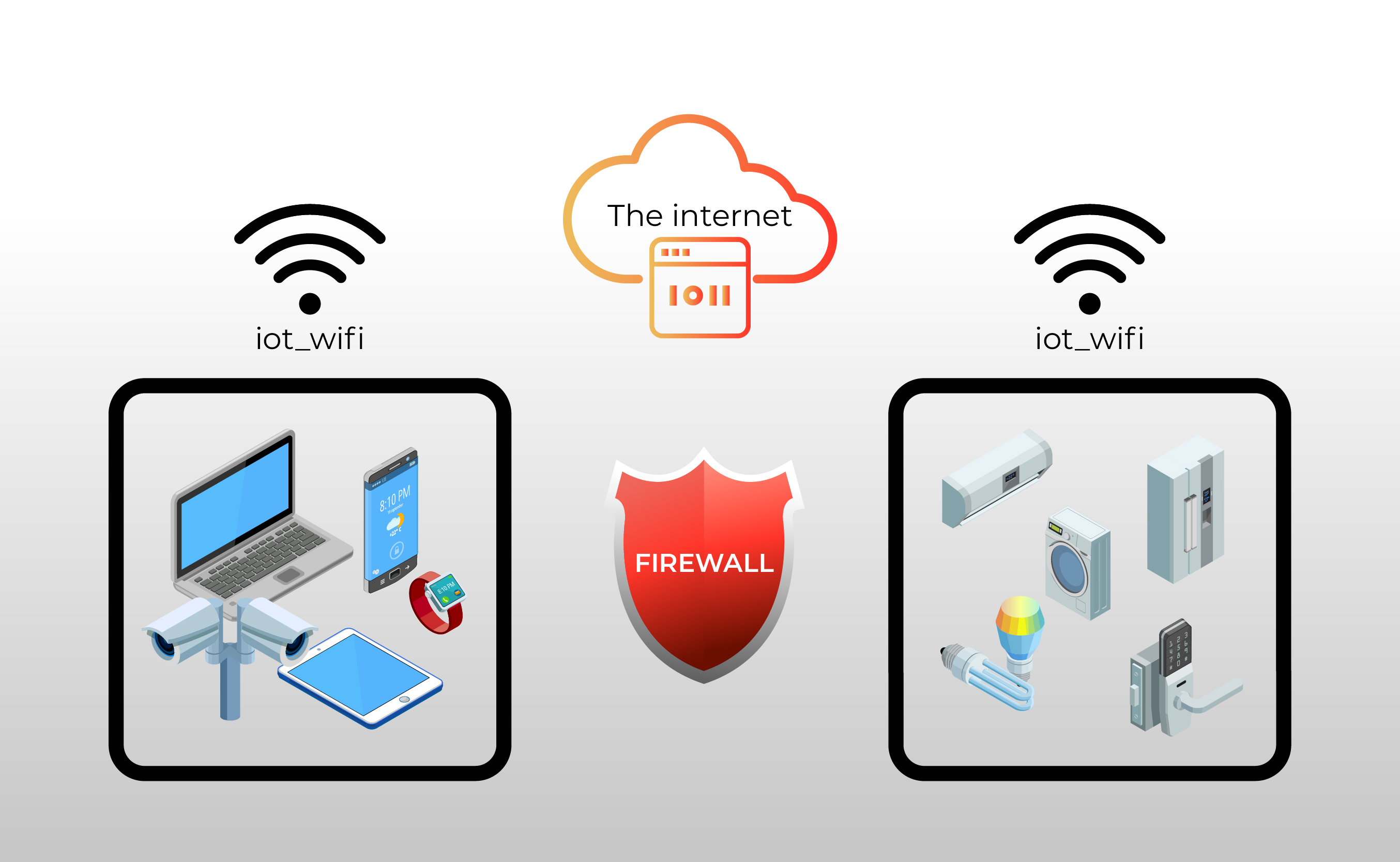
RemoteIoT behind firewall examples showcase how organizations can seamlessly integrate IoT devices while maintaining robust security protocols. In today’s interconnected world, IoT devices have become indispensable for businesses seeking to automate processes, enhance efficiency, and gather real-time insights. However, one of the most significant challenges in deploying IoT solutions is ensuring secure connectivity, especially when devices are located behind firewalls. Firewalls, while essential for protecting networks, can inadvertently block legitimate IoT traffic, making it difficult for devices to communicate with external systems. RemoteIoT addresses this challenge by offering innovative solutions that enable secure communication without compromising network integrity.
By leveraging RemoteIoT behind firewall examples, businesses can overcome these hurdles and unlock the full potential of their IoT ecosystems. These examples demonstrate how IoT devices can be securely accessed and managed even in environments with strict firewall restrictions. Whether it’s remote monitoring, data collection, or device management, RemoteIoT provides a seamless pathway for communication. This ensures that organizations can focus on deriving value from their IoT deployments without worrying about connectivity issues or security vulnerabilities.
As we delve deeper into this topic, we’ll explore real-world use cases, best practices, and strategies for implementing RemoteIoT solutions in firewall-protected environments. You’ll discover how RemoteIoT’s cutting-edge technology simplifies secure connectivity and empowers businesses to achieve their IoT goals. From industrial automation to smart cities, RemoteIoT behind firewall examples serve as a testament to the platform’s versatility and reliability. Let’s dive into the details and uncover how RemoteIoT is transforming IoT connectivity.
Read also:Exploring The Lives Of Kanye Kids A Deep Dive Into Their World
Table of Contents
- What Are the Benefits of Using RemoteIoT Behind Firewall Examples?
- How Does RemoteIoT Enable Secure Connectivity Behind Firewalls?
- Real-World Use Cases of RemoteIoT Behind Firewall Examples
- What Are the Key Features of RemoteIoT for Firewall-Protected Environments?
- How to Implement RemoteIoT in a Firewall-Protected Network?
- Challenges and Solutions for RemoteIoT Behind Firewall Examples
- Best Practices for Using RemoteIoT Behind Firewall Examples
- Frequently Asked Questions About RemoteIoT Behind Firewall Examples
What Are the Benefits of Using RemoteIoT Behind Firewall Examples?
RemoteIoT behind firewall examples offer a multitude of benefits for organizations looking to deploy IoT solutions in secure environments. One of the most significant advantages is the ability to maintain network security while enabling seamless device communication. Firewalls are designed to block unauthorized access, but this can often hinder legitimate IoT traffic. RemoteIoT addresses this issue by creating secure tunnels that bypass firewall restrictions without compromising network integrity. This ensures that IoT devices can communicate with external systems while remaining protected from potential threats.
Enhanced Security and Compliance
Security is a top priority for any IoT deployment, and RemoteIoT behind firewall examples excel in this area. By leveraging encrypted tunnels, RemoteIoT ensures that all data transmitted between IoT devices and external systems is secure. This not only protects sensitive information but also helps organizations comply with industry regulations such as GDPR and HIPAA. Additionally, RemoteIoT’s security features are designed to adapt to evolving threats, providing peace of mind for businesses operating in high-risk environments.
Increased Efficiency and Scalability
Another key benefit of RemoteIoT behind firewall examples is the ability to streamline operations and scale IoT deployments efficiently. With secure connectivity established, organizations can remotely monitor and manage devices without the need for complex configurations or manual interventions. This reduces downtime and operational costs while enabling businesses to scale their IoT ecosystems quickly. Whether it’s adding new devices or integrating with third-party systems, RemoteIoT provides the flexibility needed to meet growing demands.
How Does RemoteIoT Enable Secure Connectivity Behind Firewalls?
RemoteIoT behind firewall examples demonstrate how the platform enables secure connectivity in environments where traditional methods fall short. The key lies in its innovative architecture, which uses outbound connections to bypass firewall restrictions. Unlike inbound connections, which are often blocked by firewalls, outbound connections are typically allowed, making it easier for IoT devices to communicate with external systems. RemoteIoT leverages this approach to establish secure tunnels that facilitate seamless data exchange.
Outbound Connection Mechanism
The outbound connection mechanism is a cornerstone of RemoteIoT’s ability to work behind firewalls. By initiating connections from the IoT device to the RemoteIoT server, the platform ensures that data flows smoothly without triggering firewall alerts. This approach eliminates the need to open specific ports or configure complex firewall rules, simplifying the setup process for IT teams. Additionally, the outbound connection mechanism is designed to be lightweight, minimizing the impact on network performance.
Encryption and Authentication Protocols
Security is further enhanced through robust encryption and authentication protocols. RemoteIoT employs industry-standard encryption algorithms to protect data in transit, ensuring that it cannot be intercepted or tampered with. Authentication protocols, such as OAuth and API keys, add an extra layer of security by verifying the identity of devices and users. These measures work together to create a secure environment where IoT devices can operate without compromising network integrity.
Read also:Why Rockabye Plush Rockers Are The Perfect Gift For Kids
Real-World Use Cases of RemoteIoT Behind Firewall Examples
RemoteIoT behind firewall examples are not just theoretical concepts; they have been successfully implemented in various industries to solve real-world challenges. These use cases highlight the versatility and effectiveness of RemoteIoT in enabling secure connectivity for IoT devices. From industrial automation to healthcare, RemoteIoT has proven to be a reliable solution for organizations seeking to overcome firewall-related obstacles.
Industrial Automation
In the industrial sector, RemoteIoT behind firewall examples have transformed how manufacturers manage their IoT devices. For instance, a manufacturing plant may use IoT sensors to monitor equipment performance and predict maintenance needs. By leveraging RemoteIoT, the plant can securely access sensor data from behind its firewall, enabling real-time monitoring and analysis. This not only improves operational efficiency but also reduces downtime and maintenance costs.
Healthcare
Healthcare is another industry where RemoteIoT behind firewall examples have made a significant impact. Hospitals and clinics often rely on IoT devices to monitor patient health and manage medical equipment. However, strict firewall policies can hinder the ability to access these devices remotely. RemoteIoT addresses this challenge by providing secure connectivity that complies with healthcare regulations. This ensures that medical staff can access critical data without compromising patient privacy or network security.
What Are the Key Features of RemoteIoT for Firewall-Protected Environments?
RemoteIoT behind firewall examples are powered by a suite of features designed to address the unique challenges of firewall-protected environments. These features not only ensure secure connectivity but also enhance the overall functionality of IoT deployments. From automated configurations to real-time monitoring, RemoteIoT offers a comprehensive solution for organizations seeking to maximize the value of their IoT investments.
Automated Device Configuration
One of the standout features of RemoteIoT is its ability to automate device configuration. This eliminates the need for manual setup, reducing the risk of human error and saving valuable time for IT teams. Automated configurations are particularly beneficial in large-scale deployments, where managing hundreds or thousands of devices can be a daunting task. By streamlining the setup process, RemoteIoT enables organizations to deploy IoT solutions quickly and efficiently.
Real-Time Monitoring and Alerts
Real-time monitoring is another key feature of RemoteIoT that enhances its value in firewall-protected environments. By providing continuous visibility into device performance and network activity, RemoteIoT enables organizations to identify and address issues proactively. Alerts can be configured to notify IT teams of potential problems, such as connectivity issues or security breaches, allowing for swift resolution. This ensures that IoT deployments remain operational and secure at all times.
How to Implement RemoteIoT in a Firewall-Protected Network?
Implementing RemoteIoT in a firewall-protected network requires careful planning and execution to ensure seamless integration and optimal performance. RemoteIoT behind firewall examples provide valuable insights into the steps involved in this process, from initial setup to ongoing management. By following best practices and leveraging the platform’s features, organizations can achieve secure connectivity without compromising network integrity.
Step 1: Assess Network Requirements
The first step in implementing RemoteIoT is to assess the network requirements of your organization. This involves identifying the types of IoT devices that need to be connected, understanding the firewall policies in place, and determining the level of security needed. By conducting a thorough assessment, you can ensure that RemoteIoT is configured to meet your specific needs and align with your network architecture.
Step 2: Configure RemoteIoT Settings
Once the assessment is complete, the next step is to configure RemoteIoT settings. This includes setting up outbound connections, enabling encryption protocols, and defining authentication rules. RemoteIoT’s user-friendly interface makes it easy to configure these settings, even for IT teams with limited experience in IoT deployments. Additionally, the platform provides detailed documentation and support to guide users through the process.
Challenges and Solutions for RemoteIoT Behind Firewall Examples
While RemoteIoT behind firewall examples offer numerous benefits, organizations may encounter challenges during implementation. These challenges can range from technical issues to organizational resistance, but they can be overcome with the right strategies and solutions. By understanding the potential obstacles and preparing for them in advance, businesses can ensure a smooth and successful deployment.
Challenge 1: Firewall Configuration
One of the most common challenges is configuring firewalls to allow outbound connections without compromising security. This requires a deep understanding of firewall policies and the ability to balance security with functionality. RemoteIoT addresses this challenge by providing detailed guidelines and support for firewall configuration, ensuring that organizations can achieve the desired level of connectivity without exposing their networks to unnecessary risks.
Challenge 2: Device Compatibility
Another challenge is ensuring compatibility with a wide range of IoT devices. Different devices may have varying requirements and limitations, making it difficult to establish a standardized approach. RemoteIoT overcomes this challenge by supporting a broad range of devices and protocols, enabling organizations to connect and manage their IoT ecosystems seamlessly.
Best Practices for Using RemoteIoT Behind Firewall Examples
To maximize the benefits of RemoteIoT behind firewall examples, organizations should follow best practices that enhance security, efficiency, and scalability. These practices are based on real-world experience and insights from industry experts, ensuring that businesses can achieve optimal results from their IoT deployments.
Practice 1: Regularly Update Security Protocols
Security is an ongoing process, and organizations should regularly update their security protocols to address emerging threats. This includes implementing the latest encryption algorithms, updating authentication rules, and conducting regular security audits. By staying proactive, businesses can ensure that their IoT deployments remain secure and compliant with industry standards.
Practice 2: Monitor Network Performance
Monitoring network performance is essential for identifying and resolving issues before they impact operations. RemoteIoT provides tools for real-time monitoring and analysis, enabling organizations to track device performance and network activity. By leveraging these tools, businesses can optimize their IoT deployments and ensure that they continue to deliver value over time.
Frequently Asked Questions About RemoteIoT Behind Firewall Examples
How Does RemoteIoT Handle Firewall Restrictions?
RemoteIoT uses outbound connections to bypass firewall restrictions, ensuring secure communication without compromising network integrity.
Is RemoteIoT Compatible with All IoT Devices?
Yes, RemoteIoT supports a wide range of IoT devices and protocols, making it compatible with most devices on the market.
What Are the Costs Associated with RemoteIoT?
RemoteIoT offers flexible pricing plans based on the scale of deployment and specific organizational needs. Contact their sales team for detailed pricing information.
In conclusion, RemoteIoT behind firewall examples provide a powerful solution for organizations seeking to deploy IoT devices in secure environments. By leveraging innovative technology and best practices, businesses can achieve seamless connectivity,